GLOBAL GUARD MEETING
December 8, 1998
3085 ENG II
9:00 - 10:00
In attendance:
Karl Levitt (KL), David Klotz (DK), David O'Brien (DOB), and Jeff Rowe
(JR)
TOPICS
PI Meeting Presentation Ideas
Paprika Attack
Additional Ideas for Global Guard
For Next Weeks PI Meeting
-
PI Meeting Presentation Ideas
-
KL: Viewgraphs and scenarios with correlation
-
David O'Brien explains CIDF and potential direction for Global Guard
-
DOB has concerns about:
-
Yemini model how many attacks it can detect
-
Cant express everything in terms of SEMS
-
Build in Tripwire
-
A problem with a single symptom creates a disconnected graph
-
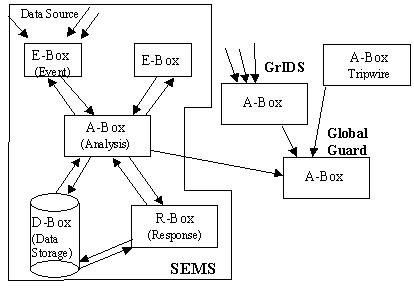
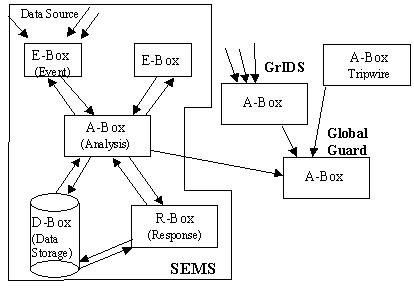
Global Guard take CIDF view; make Smart Event Management System (SEMS),
detect XYZ attack in SEMS model
-
Augment SEMS for intrusion detection and response
-
Codebook
-
Paprika Attack
-
DOB: Linux machine attacked causing network performance problems: response
times were slow, packets were missing caused by hackers overloading the
routers
-
SEMS would have misdiagnosed the problem as congested routers or a bad
router card
-
JR: Use sniffer, profile peoples traffic?
-
DOB: Set threshold: Machines using 80% bandwidth over 10 minute period.
Our collision rates are too high.
-
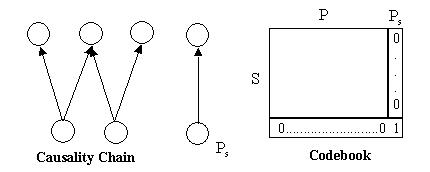
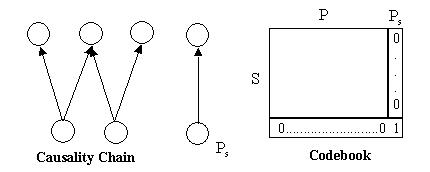
Causality Chain leads to codebook. What is there is a problem that doesnt
have any redundancy in its symptoms?
-
DOB: Use SEMS for things with a "natural fit."
-
Will have to augment some problems
-
Modeling language
-
KL: Correlation attacks formulate using SEMS?
-
JR: Still use codebook approach to correlation
-
Additional Ideas for Global Guard
-
DOB: Correlation Aggregation
-
Upper level A-Box to take in data sources
-
A-box tripwire
-
Aggregate codebook in Global Guard
-
To reduce false positives, use multiple IDS
-
For Next Weeks PI Meeting
-
Roughly encode with SEMS by Friday
-
Scenario à Causality Graph à
Codebook
-
Spend 5 minutes talking about why we need correlation
-
SEMS faster at rulesets than GrIDS because of the codebook
-
SEMS has optimization
-
GrIDS cant do aggregation
-
Codebook correlations and correlation of the correlations
-
KL: Permutation matrix redundancy level now, need for error detection
-
Models
-
Model generic attacks network, host, DOS, protocol based (SYN-FLOOD)
-
Multistage attack, coordinated attacks, distributed attacks
-
DK: Model symptoms
-
Model Attackers
-
Certain symptoms he can change
-
What symptoms he can make us see
-
Attacker can make attack look like a network problem
-
Attacker misleads different host
-
Access IDS vulnerabilities based on attacks
-
Embellish Paprika attack
-
Piecing together attacks hierarchical problem.